It’s said that ‘Google before you Tweet’ is the new ‘Think Before You Speak’. Living and breathing this very adage are today’s millennials. Hence the runaway success and the response generated by a recent poster presentation on campus about ‘Privacy and Security in Online Social Media’ comes as no surprise. Let’s see what the buzz was about.
Recently, students of an elective course on online social media came together to present their projects through uniquely designed posters. The course itself on ‘Privacy and Security in Online Social Media’ covered a gamut of topics that are relevant today such as general social networks and their increasing popularity, privacy and security issues in such networks, propagation of fake content particularly fake news, misinformation or credibility of online information, creating profiles from social media activity like Facebook posts, tweets and others, how social media is being used by governmental organizations such as the Police force, analysis of social media strategies adopted by various ministries, analysis of anonymous networks, and so on.
Visiting Professor Ponnurangam Kumaraguru (also known as PK) who taught this course says that among other topics, they studied various social media strategies of different organizations that could lead to virality of content posted. Giving a real example of the application of the coursework he said, “Take the case of traffic management; the police are actually looking at technologies that can highlight posts where there is actionable information, or a method that will sift through all the online information and tell them that these posts (x) are more important than others (y). Because if a person is manually going through the online content, spending equal amount of resources on all posts where they are tagged, then there may be more important things that are left out.”
Here’s a brief roundup of some of the interesting projects students worked on:
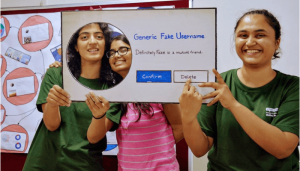
One Phish Two Phish
Phishing through email is passe. Hackers now use social networking sites such as Facebook, LinkedIn, Twitter and others to obtain sensitive information or to lure you to click malicious links. To test the vulnerability and to find the level of susceptibility of their peers to phishing attacks, students Soumya Vaddlamannati and Soujanya Chandrashekhar conducted an experiment by creating a fake account on Facebook and sending out around 200 friend requests to their batchmates. Similarly they created another LinkedIn phishing trail by using a plugin that simulates the behaviour of a LinkedIn user to automate sending invitations. They then tracked and analysed responses to these requests.
Blab on Gab
Gab has been called a “Twitter for Racists”. Because unlike Twitter and other social media networks that have rules and abide by standards, this social media platform for white nationalists and the alt-right allows users to say anything they want. It shot into notorious limelight in the aftermath of the bloody shooting at a synagogue in Pittsburgh recently. The shooter Robert Bowers was an avid user of Gab and had just hours before the shooting posted anti-semitic comments on the platform. Dheeraj Reddy Pailla who had begun analyzing content on Gab before the deadly incident says that the urgency to analyze such vitriolic and hate-speech became all the more evident after the shooting. Analyzing such posts both in English and other regional languages can be very useful and informative for security agencies.

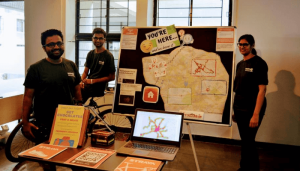
Bike More Reveal More
Strava is an online fitness tracker application which works as the Facebook for athletes. While it may be tempting to share (or boast of) running or biking workouts on it, students worked on analyzing how sensitive user information such as their location can be compromised. They used biking habits of Strava users whose information was publicly available to find the home address or location of the users.
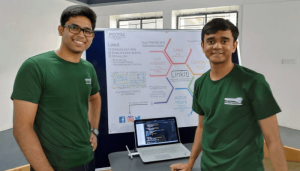
True or False
In this project, students analysed the profiles on both LinkedIn and Facebook to verify whether the statement “Interned at Google” on LinkedIn was really valid. They used users’ Facebook posts to make this comparison.
Not Safe For Work
To weed out objectionable content, students built a browser plugin which would analyse the posts on Reddit, filter those that are Not Safe For Work (NSFW) by automatically deleting them, thereby sanitizing content for the workplace.
Dance of Democracy
In view of the upcoming national elections in 2019, students used Twitter data to predict votes for the two main national parties.
Others
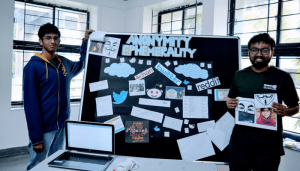
There were other interesting projects too on finding our the network graph of students from one of their batches, anonymising the pictures uploaded on social media to not reveal the location; analysing the Russian trolls data, and a project on anonymised networks like 4Chan.
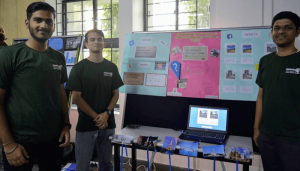
Art, Paper, Scissor
The poster presentation showcasing these projects itself was unique in that it eschewed the typical route and went the old school way by encouraging hands-on creativity. “Sir told us he didn’t want a typical printout with Method, Objective and Result. We were asked to use sketch pens, scissors and chart paper. Basically the mandate was to be as creative as possible by using anything you want. The intent was to attract as many people as we could and make the presentation interactive,” says another student Devansh Manu. They were evaluated by external jury members who walked up to the stalls without a formal invitation.

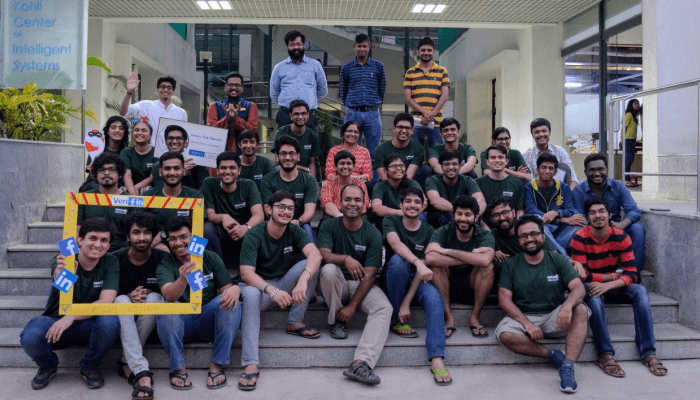
From The Horse’s Mouth
Speaking about the popularity of the course, PK says, “The course goes amazingly well with students because that’s what they do otherwise!” Terming it as a learning experience for himself each time he’s taught the course, PK adds, “I wasn’t aware of some of the social media networks such as Gab or Strava.”According to Dheeraj who worked on the Gab project, “One of the most defining aspects of the course is its ability to remain as close to reality as possible. We had a lot of fun throughout the course, with PK at the centre of some timely humour during classes. I would say it’s definitely one of the best courses I’ve taken and a fantastic experience.” Soumya chimes in saying,”Most professors complain about the lack of enthusiasm among students of this generation, but this course had us reading up on articles and papers, which we would then discuss and debate over in class. From learning to crawl Twitter for data to having guest lecturers from CMU like Alessandro Acquisti, the course seemed to have it all.” For PK himself, the goal of the course is to get students to understand the ramifications of being in an online world. “Where ever the students go work later, like on a product, they will understand privacy concerns and apply the things learned,” he states.

To see more about the event, please visit:
https://www.facebook.com/media/set/?set=a.2490167361008562&type=1&l=9dbbc363c0


Next post